
Bug Bounty Programs
- Posted by 3.0 University
- Categories Cyber Security
- Date April 12, 2026
- Comments 0 comment
Bug Bounty Programs Explained: A Beginner’s Guide to Getting Paid to Find Security Bugs (2026)
Imagine getting paid, legally to break into Apple, Google, or Meta.
No office. No boss. No fixed hours. Just you, a laptop, and the skill to find what the company’s own engineers missed.
That’s what bug bounty programs are, and in 2026 they’ve quietly become one of the most practical entry points into a cybersecurity career. Apple currently pays up to $200,000 for critical firmware flaws.
Microsoft’s 2025 Zero Day Quest event paid out over $1.6 million in a single focused campaign. Immunefi, which runs bounties for Web3 companies, has paid critical-bug rewards as high as $1 million.
And here’s the part nobody tells you: you don’t need a computer science degree to start.
This guide breaks down exactly what a bug bounty program is, how it works, how much beginners can realistically earn, and the step-by-step path to land your first valid report. No fluff. No hype.
What Is a Bug Bounty?
A bug bounty is a cash reward a company pays to someone outside the company who finds a security flaw in its website, app, or system — and reports it responsibly instead of exploiting it.
Think of it like this: a bank hires a locksmith to legally try breaking into its vault. If the locksmith finds a weak lock, the bank fixes it and pays the locksmith for the heads-up. That’s a bug bounty, only the “vault” is a login page, an API, or a mobile app.
The people who do this work are called ethical hackers, security researchers, or white-hat hackers.
The companies running the programs include almost every big tech name you know Google, Meta, Apple, Microsoft, Uber, Dropbox, Shopify, and thousands more.
What Is Bug Hunting in Cybersecurity?
Bug hunting is the hands-on process of searching a system for security weaknesses.
These weaknesses can look like:
- A login form that accepts an SQL injection and leaks user data
- An API endpoint that lets one user see another user’s private information (IDOR)
- A comment box that runs hidden JavaScript (cross-site scripting, or XSS)
- A misconfigured cloud storage bucket exposing internal files
- A forgotten subdomain pointing to a service the company no longer owns (subdomain takeover)
A bug hunter’s job is to find these issues before a criminal does, write a clear report explaining what the problem is, and help the company fix it. In exchange, the company pays a bounty scaled to how bad the bug is.
What Is a Bug Bounty Program?
A bug bounty program is the structured system a company uses to invite outside hackers to test its defences.
It answers three questions upfront:
- What’s in scope — which websites, apps, and APIs you’re allowed to test
- What counts as a valid bug — and what doesn’t (spam reports, known issues, etc.)
- How much each severity level pays — from low ($50–$500) to critical ($10,000–$200,000+)
Most programs run through dedicated platforms rather than directly. The big four you should know:
- HackerOne — the largest platform, home to Google, Uber, Dropbox, the U.S. Department of Defense, and 2,000+ other programs. Average mid-severity payout: $500–$5,000.
- Bugcrowd — second-biggest globally. Average payout: $300–$3,000. Top payouts: $50,000+.
- Intigriti — Europe-focused, beginner-friendly onboarding, fast triage. Nvidia launched its program here in 2025.
- Immunefi — the Web3 and smart-contract leader. Average critical-bug payout: $13,000. Median confirmed report: $2,000.

How Do Bug Bounty Programs Work? (The 5-Step Flow)
Here’s what actually happens, start to finish:
Step 1 — Scope definition
The company publishes a policy that lists which assets you can test (for example: *.companyname.com, their iOS app, their public API). Anything not listed is off-limits.
Step 2 — You register and agree to the rules-
On HackerOne or Bugcrowd, this takes about two minutes. Public programs let anyone start hunting; private ones are invite-only and usually pay more.
Step 3 — You hunt
You probe the in-scope assets, looking for flaws. Most hunters use Burp Suite (free version is enough to start), browser developer tools, and a bit of Python scripting.
Step 4 — You report
When you find something real, you write it up — clear steps to reproduce, a short proof-of-concept, and why it matters to the business. A good report is what gets you paid.
Step 5 — Triage and payout
The company’s security team verifies your finding, classifies its severity, fixes it, and sends you the bounty. Fast programs pay within two weeks. On HackerOne’s Temu program, for example, the average time from report to bounty decision is roughly two weeks.
How Much Can Beginners Actually Earn? (Real 2026 Numbers)
Let’s skip the “you can make millions” clickbait.
Here’s the honest picture:
- Your first valid bug usually takes 4–12 weeks of consistent practice. First payouts are typically $50–$500 — often duplicates or low-severity issues.
- By month 6, consistent beginners who specialise (say, in web APIs or IDOR bugs) report earning $500–$3,000 per month on the side.
- Critical bugs at top programs pay $10,000–$100,000+. These are rare and competitive.
- Smart contract / Web3 bugs pay the most — Scroll (a Layer-2 blockchain) set a critical bug cap of $1,000,000 in 2025. Ethereum projects have collectively paid over $7.6 million in bug bounties.
One reality check: platforms report that 50–70% of submitted bug bounty reports are rejected (duplicates, out-of-scope, false positives). Only about 5% of all reports are classified as critical severity. This is a long-game field, not a weekend side hustle.
Bug Bounty Programs for Beginners: A 6-Step Starter Plan
If you’re starting from zero, here’s the path that actually works in 2026.
Step 1: Get the web fundamentals down
Before you touch a target, you need to understand how the web really works:
- HTTP requests and responses, headers, cookies
- How authentication works (sessions, JWT tokens, OAuth)
- Basic JavaScript and how browsers talk to servers
- The OWASP Top 10 the industry’s list of the most common web vulnerabilities
Free resources: PortSwigger Web Security Academy (the gold standard), TryHackMe beginner rooms, and OWASP’s official cheat sheets.
Step 2: Learn the bugs that pay beginners
Don’t chase exotic zero-days in your first month. Focus on these beginner-friendly bug classes:
- IDOR (Insecure Direct Object Reference) — changing user_id=123 to user_id=124 and seeing someone else’s data
- XSS (Cross-Site Scripting) — injecting JavaScript into input fields
- Open redirects — tricking a URL to send users to an attacker’s site
- Misconfigured CORS
- Information disclosure — exposed debug endpoints, API keys in JavaScript files, leaked .env files
These won’t make you famous, but they pay and they teach pattern recognition.
Step 3: Master one tool — Burp Suite
Burp Suite Community Edition is free. It sits between your browser and the target website and lets you see and modify every request. Most experienced bug hunters say the same thing: if you’re not using Burp, you’re missing roughly 70% of what’s actually happening.
Spend two weeks just learning the Proxy, Repeater, and Intruder tabs. That’s enough for your first year.
Step 4: Pick ONE program and go deep
The biggest beginner mistake is hopping between 20 programs in a week. Experienced hunters pick one target and study it for weeks.
Good first-program filters on HackerOne or Bugcrowd:
- Public (not invite-only)
- Clear, simple scope
- “Beginner-friendly” or Vulnerability Disclosure Program (VDP) tag
- Not a massive target like Google (too many hunters, everything’s already found)
Step 5: Write reports that get paid
Even a real bug gets rejected if the report is sloppy. A good report has:
- A one-line summary of the bug and its impact
- Numbered steps to reproduce — copy-pasteable
- A minimal proof-of-concept — curl command, screenshot, or 30-second video
- Business impact — why this matters (data leak? account takeover? financial loss?)
- Suggested fix — optional but it shows you understand the problem
Before hitting submit, ask yourself: If I were the developer reading this, could I fix the bug using only what I’ve written? If no, rewrite.
Step 6: Stay consistent for 90 days minimum
Most beginners quit between week 6 and week 10, right before the first valid bug shows up. Treat the first three months as learning, not earning. The money comes after the pattern recognition does.
Real-World Example: How a Researcher Refused $0 and Still Made the News
In 2023, independent researcher Justin Steven found a DOM-based cross-site scripting vulnerability in Gartner’s Peer Insights marketing widget. The company’s private bug bounty program had terms preventing him from publicly disclosing the technical details.
Instead of accepting a quiet payout, Steven published the vulnerability anyway, forfeiting the reward. His reasoning: the security community benefits more from open knowledge than from a locked-up paycheck.
The story illustrates something important for beginners — bug bounty culture rewards integrity and transparency as much as skill. Your reputation on these platforms travels with you and compounds over years.
Why Bug Bounty Programs Matter in 2026?
The case for running a bug bounty program is simple economics. Web3 losses alone hit $2.05 billion in Q1 2025, with access-control flaws accounting for $1.63 billion of that, according to data from Hacken and FailSafe. A bounty program that pays $50,000 for a critical report can prevent a $50 million breach.
For hackers, the attack surface keeps expanding. Companies are shipping microservices, complex APIs, cloud stacks, and now AI systems faster than they can secure them.
Prompt injection- attacking AI model logic is one of the fastest-growing bug categories in 2025–2026, and Google, Apple, and Nvidia now run AI-specific bounties. For beginners entering the field today, there’s more surface to test than at any point in the last decade.
Frequently Asked Questions
Is bug bounty hunting legal?
Yes — as long as you only test systems you have written permission to test (that’s what a bug bounty program is), and you stay within the defined scope. Testing anything outside the scope is illegal and can get you banned or prosecuted.
Do I need a degree or certification to start?
No. Most top hunters are self-taught. Certifications like OSCP or eWPTX can help if you want to apply to invite-only platforms like Synack later, but they’re not required to earn your first bounty.
How long until I find my first bug?
Realistically, 4–12 weeks of consistent daily practice for most beginners. Some find one in week two. Some take six months. The variable is recon quality and report clarity, not luck.
Is bug bounty income taxable in India?
Yes. Bug bounty rewards are treated as income and must be declared. Most platforms pay in USD via PayPal or direct bank transfer, which adds a foreign-remittance layer. Consult a CA for specifics.
Can I do bug bounty while having a full-time job?
Yes — the majority of bug hunters on HackerOne and Bugcrowd are part-time. Most treat it as a paid learning path that sharpens skills they also use at work.
Which platform should I start with?
HackerOne for the largest program selection, or Intigriti if you want the smoothest beginner onboarding and faster triage. Skip Synack and Cobalt until you have a year of experience.
Final Thoughts
Bug bounty programs aren’t a get-rich-quick scheme. They’re a legitimate, globally recognised path into cybersecurity where your skill and persistence matter more than your résumé.
The hunters who succeed aren’t the most talented they’re the most consistent. They read every program policy. They go deep on one target instead of skimming twenty. They write reports a tired triage engineer can validate in five minutes.
If that sounds like the kind of work you’d enjoy, the tools are free, the platforms are open, and the attack surface is bigger than ever.
Ready to turn bug hunting into a structured skillset?
Explore 3.0 University’s Certified Ethical Hacker Program and Certification Program in Offensive Cyber Techniques to build the foundation that serious bug bounty hunters use.
You may also like
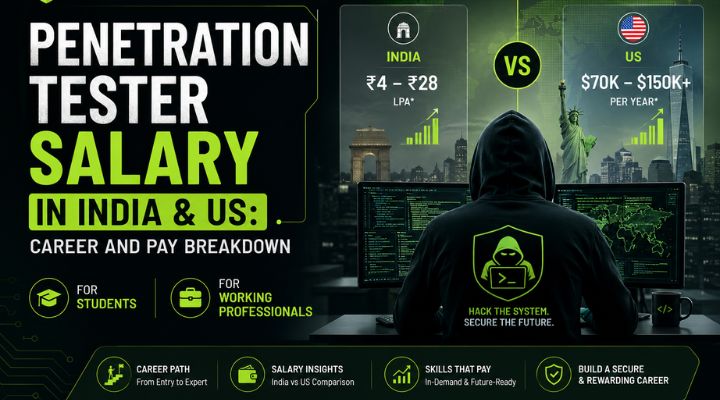
How Much Does a Penetration Tester Earn in 2026?


